SessionShark, How Attackers Bypass MFA for Office365 and How to Defend Against It
SessionShark: How Attackers Bypass MFA and How to Defend Against It
Introduction
Multi-Factor Authentication (MFA) has long been considered a crucial layer of defense in securing online accounts. However, recent developments in phishing-as-a-service (PhaaS) platforms such as SessionShark have demonstrated that even MFA is not impervious to compromise. SessionShark is a sophisticated phishing toolkit that enables cybercriminals to bypass MFA protections, particularly targeting Microsoft Office 365 environments. This article explores how SessionShark operates, how it manages to bypass MFA, and what organizations can do to mitigate the risk.
How SessionShark Bypasses MFA
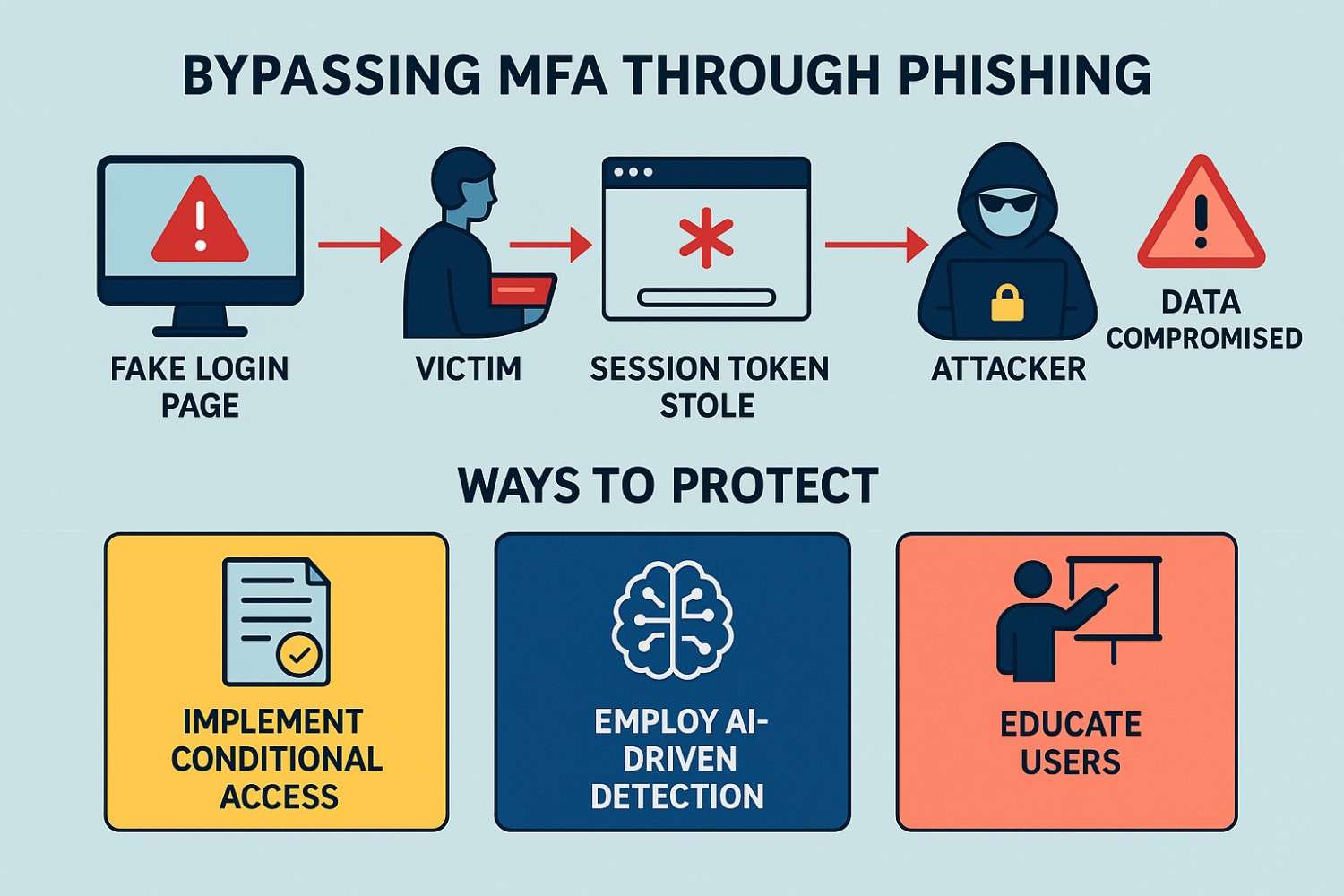
SessionShark uses an adversary-in-the-middle (AiTM) attack technique, which allows it to steal authenticated session tokens in real-time. Here’s a detailed breakdown of its operation:
Phishing Page Deployment
Attackers create convincing fake login pages that mirror legitimate Microsoft Office 365 authentication portals. Victims are tricked into entering their credentials and completing the MFA process without realizing they are interacting with a malicious site (SC World, 2024).Session Token Theft
After the victim successfully authenticates (even completing MFA), SessionShark captures the session cookie or token. This token represents the victim’s authenticated session and can be reused by the attacker to access the account without needing the victim’s password or second authentication factor (Dark Reading, 2024).Real-Time Exfiltration
SessionShark immediately sends the stolen session token to attackers, often using integrated Telegram bots. This allows cybercriminals to hijack the session almost instantly before any defenses can detect unusual activity (HackRead, 2024).Advanced Evasion Tactics
SessionShark employs multiple methods to avoid detection, including:- Using Cloudflare to obscure the hosting infrastructure
- Anti-bot and anti-crawler scripts to prevent automated security systems from accessing the phishing pages
- Highly customizable configurations to bypass traditional signature-based detection systems (SC World, 2024).
Why This Method is Dangerous
Traditional MFA systems protect against attackers who have only stolen a password. However, if an attacker can steal a session token after authentication, they no longer need the password or MFA code. This fundamentally undermines one of the strongest protections that organizations rely on today.
Mitigation Strategies
To defend against advanced attacks like those enabled by SessionShark, organizations must layer their defenses and not rely solely on MFA:
Implement Conditional Access Policies
Use conditional access that evaluates the risk based on context, such as device compliance, geographic location, and sign-in behavior. Block or challenge risky sign-ins even if they have valid credentials and tokens.Leverage AI-Driven Threat Detection
Traditional phishing detection often fails against real-time AiTM attacks. Deploy AI-based systems that can detect subtle phishing behaviors and token anomalies (SlashNext, 2024).User Training and Awareness
Regularly educate users about the dangers of phishing and how to verify URLs before entering credentials. Even the best technical defenses can fail if users are unaware.Monitor for Unusual Sessions
Set up continuous monitoring for suspicious login activities, such as sessions being accessed from unexpected locations or devices.Shorten Session Lifetimes
Configure systems to shorten the validity period of authentication tokens. This reduces the window of opportunity for attackers who manage to steal a session.Use Phishing-Resistant MFA
Implement technologies like FIDO2 security keys or certificate-based authentication that are resistant to man-in-the-middle and token theft attacks.
Conclusion
SessionShark highlights a critical evolution in cyberattack techniques. By targeting session tokens instead of credentials, it renders traditional MFA less effective. Organizations must adapt by combining strong technical defenses, intelligent monitoring, and user education to stay ahead of such sophisticated threats.
References
Dark Reading. (2024, April 25). SessionShark Phishing Toolkit Can Steal MFA-Protected Sessions. Retrieved from https://www.darkreading.com/remote-workforce/sessionshark-toolkit-microsoft-365-steal-tokens
HackRead. (2024, April 24). SessionShark Phishing Kit Bypasses MFA to Steal Office 365 Logins. Retrieved from https://hackread.com/sessionshark-phishing-kit-bypass-mfa-steal-office-365-logins/
SC World. (2024, April 25). Microsoft Office 365 MFA Targeted by SessionShark Phishing Kit. Retrieved from https://www.scworld.com/news/microsoft-office-365-mfa-targeted-by-sessionshark-phishing-kit
SlashNext. (2024, April 25). SessionShark Steals Session Tokens to Slip Past Office 365 MFA. Retrieved from https://slashnext.com/blog/sessionshark-steals-session-tokens-to-slip-past-office-365-mfa/